What is DevSecOps? A Guide to Building Secure Software
The Essential Guide to Requirements Management and Traceability
Chapters
- 1. Requirements Management
- Overview
- 1 What is Requirements Management? A Complete Guide
- 2 Why do you need Requirements Management?
- 3 Four Stages of Requirements Management Processes
- 4 Adopting an Agile Approach to Requirements Management
- 5 Status Request Changes
- 6 Conquering the 5 Biggest Challenges of Requirements Management
- 7 Three Reasons You Need a Requirements Management Solution
- 8 Guide to Poor Requirements: Identify Causes, Repercussions, and How to Fix Them
- 2. Writing Requirements
- Overview
- 1 Functional requirements examples and templates
- 2 What Is a Product Requirements Document? A Complete PRD Guide
- 3 What Is a User Requirement Specification (URS)? How to Write and Manage One
- 4 Identifying and Measuring Requirements Quality
- 5 How to Write a System Requirements Specification (SRS) Document
- 6 The Fundamentals of Business Requirements: Examples of Business Requirements and the Importance of Excellence
- 7 What Is a Compliance Risk Assessment? Steps, Framework, and Examples
- 8 Adopting the EARS Notation to Improve Requirements Engineering
- 9 Jama Connect Advisor™
- 10 Frequently Asked Questions about the EARS Notation and Jama Connect Advisor™
- 11 How to Write an Effective Product Requirements Document (PRD)
- 12 Functional vs. Non-Functional Requirements
- 13 What Are Nonfunctional Requirements and How Do They Impact Product Development?
- 14 What Is a Software Design Specification? Key Components + Template
- 15 Characteristics of Effective Software Requirements and Software Requirements Specifications (SRS)
- 16 8 Do’s and Don’ts for Writing Requirements
- 17 Project Requirements: Types, Process, and Best Practices
- 3. Requirements Gathering and Management Processes
- Overview
- 1 Requirements Engineering
- 2 Requirements Analysis
- 3 A Guide to Requirements Elicitation for Product Teams
- 4 Requirements Gathering Techniques for Agile Product Teams
- 5 Requirements Gathering in Software Engineering: Process, Techniques, and Best Practices
- 6 Defining and Implementing a Requirements Baseline
- 7 Managing Project Scope — Why It Matters and Best Practices
- 8 How Long Do Requirements Take?
- 9 How to Reuse Requirements Across Multiple Products
- 4. Requirements Traceability
- Overview
- 1 What is Requirements Traceability? Importance Explained
- 2 Tracing Your Way to Success: The Crucial Role of Traceability in Modern Product and Systems Development
- 3 Bidirectional Traceability: What It Is and How to Implement It
- 4 What is Engineering Change Management (ECM)? A Complete Guide
- 5 Change Impact Analysis (CIA): A Short Guide for Effective Implementation
- 6 What is Meant by Version Control?
- 7 Key Traceability Challenges and Tips for Ensuring Accountability and Efficiency
- 8 The Role of a Data Thread in Product and Software Development
- 9 Unraveling the Digital Thread: Enhancing Connectivity and Efficiency
- 10 What is a Traceability Matrix? A Guide to Requirements Traceability
- 11 How to Create and Use a Requirements Traceability Matrix (RTM)
- 12 Traceability Matrix 101: Why It’s Not the Ultimate Solution for Managing Requirements
- 13 Live Traceability vs. After-the-Fact Traceability
- 14 Overcoming Barriers to Live Requirements Traceability™
- 15 Requirements Traceability, What Are You Missing?
- 16 Four Best Practices for Requirements Traceability
- 17 Requirements Traceability: Links in the Chain
- 18 What Are the Benefits of End-to-End Traceability During Product Development?
- 19 FAQs About Requirements Traceability
- 20 Product Traceability for Regulated Industries: A Complete Guide to Audit-Ready Compliance
- 5. Requirements Management Tools and Software
- Overview
- 1 Selecting the Right Requirements Management Tools and Software
- 2 Why Investing in Requirements Management Software Makes Business Sense During an Economic Downturn
- 3 Why Word and Excel Alone is Not Enough for Product, Software, and Systems Development
- 4 Can You Track Requirements in Excel?
- 5 What Is Application Lifecycle Management (ALM)?
- 6 Is There Life After DOORS®?
- 7 Can You Track Requirements in Jira?
- 8 Checklist: Selecting a Requirements Management Tool
- 6. Requirements Validation and Verification
- 7. Meeting Regulatory Compliance and Industry Standards
- Overview
- 1 Understanding ISO Standards
- 2 Understanding ISO/IEC 27001: A Guide to Information Security Management
- 3 What is DevSecOps? A Guide to Building Secure Software
- 4 Compliance Management
- 5 What Is Functional Safety (FuSa)? Standards, Lifecycle, and Where Programs Fail
- 6 What is FMEA? Failure Mode and Effects Analysis Guide
- 7 TÜV SÜD: Ensuring Safety, Quality, and Sustainability Worldwide
- 8 What is IEC 62443? A Guide to Industrial Cybersecurity
- 8. Systems Engineering
- Overview
- 1 What is Systems Engineering?
- 2 How Do Engineers Collaborate? A Guide to Streamlined Teamwork and Innovation
- 3 The Systems Engineering Body of Knowledge (SEBoK)
- 4 What Is MBSE? Model-Based Systems Engineering Explained
- 5 Digital Engineering Between Government and Contractors
- 6 Digital Engineering Tools: The Key to Driving Innovation and Efficiency in Complex Systems
- 9. Automotive Development
- Overview
- 1 Understanding IATF 16949: A Quick Guide to Automotive Quality Management
- 2 What Is ISO 21434? Automotive Cybersecurity Engineering Explained
- 3 What Is ISO 26262? A Guide to Functional Safety in Automotive
- 4 What Is ASIL? A Guide to Automotive Safety Integrity Levels in ISO 26262
- 5 What Is SOTIF? A Guide to ISO 21448 for ADAS Safety
- 10. Medical Device & Life Sciences Development
- Overview
- 1 The Importance of Benefit-Risk Analysis in Medical Device Development
- 2 Software as a Medical Device: Revolutionizing Healthcare
- 3 What’s a Design History File, and How Are DHFs Used by Product Teams?
- 4 Navigating the Risks of Software of Unknown Pedigree (SOUP) in the Medical Device & Life Sciences Industry
- 5 What Is ISO 13485? A Guide to Medical Device Quality Management Systems
- 6 What You Need to Know: ANSI/AAMI SW96:2023 — Medical Device Security
- 7 ISO 13485 vs ISO 9001: Understanding the Differences and Synergies
- 8 What Is IEC 62304? A Guide to Medical Device Software
- 9 What Is a Device Master Record (DMR)? Definition and FDA Requirements
- 10 Failure Modes, Effects, and Diagnostic Analysis (FMEDA) for Medical Devices: What You Need to Know
- 11 Embracing the Future of Healthcare: Exploring the Internet of Medical Things (IoMT)
- 12 What Is General Safety and Performance Requirements (GSPR)? What You Need To Know
- 13 What Is IEC 62366? A Guide to Medical Device Usability Engineering
- 11. Aerospace & Defense Development
- Overview
- 1 What Is ARP4754A? A Complete Guide to Civil Aircraft and Systems Development Assurance
- 2 Understanding ARP4761A: Guidelines for System Safety Assessment in Aerospace
- 3 What Is DO-254? A Complete Guide to Airborne Hardware Design Assurance
- 4 What Is DO-178C? A Complete Guide to Airborne Software Certification
- 12. Architecture, Engineering, and Construction (AEC industry) Development
- 13. Industrial Manufacturing & Machinery, Automation & Robotics, Consumer Electronics, and Energy
- 14. Semiconductor Development
- 15. AI in Product Development
- 16. Risk Management
- 17. Product Development Terms and Definitions
Chapter 7: What is DevSecOps? A Guide to Building Secure Software
Chapters
- 1. Requirements Management
- Overview
- 1 What is Requirements Management? A Complete Guide
- 2 Why do you need Requirements Management?
- 3 Four Stages of Requirements Management Processes
- 4 Adopting an Agile Approach to Requirements Management
- 5 Status Request Changes
- 6 Conquering the 5 Biggest Challenges of Requirements Management
- 7 Three Reasons You Need a Requirements Management Solution
- 8 Guide to Poor Requirements: Identify Causes, Repercussions, and How to Fix Them
- 2. Writing Requirements
- Overview
- 1 Functional requirements examples and templates
- 2 What Is a Product Requirements Document? A Complete PRD Guide
- 3 What Is a User Requirement Specification (URS)? How to Write and Manage One
- 4 Identifying and Measuring Requirements Quality
- 5 How to Write a System Requirements Specification (SRS) Document
- 6 The Fundamentals of Business Requirements: Examples of Business Requirements and the Importance of Excellence
- 7 What Is a Compliance Risk Assessment? Steps, Framework, and Examples
- 8 Adopting the EARS Notation to Improve Requirements Engineering
- 9 Jama Connect Advisor™
- 10 Frequently Asked Questions about the EARS Notation and Jama Connect Advisor™
- 11 How to Write an Effective Product Requirements Document (PRD)
- 12 Functional vs. Non-Functional Requirements
- 13 What Are Nonfunctional Requirements and How Do They Impact Product Development?
- 14 What Is a Software Design Specification? Key Components + Template
- 15 Characteristics of Effective Software Requirements and Software Requirements Specifications (SRS)
- 16 8 Do’s and Don’ts for Writing Requirements
- 17 Project Requirements: Types, Process, and Best Practices
- 3. Requirements Gathering and Management Processes
- Overview
- 1 Requirements Engineering
- 2 Requirements Analysis
- 3 A Guide to Requirements Elicitation for Product Teams
- 4 Requirements Gathering Techniques for Agile Product Teams
- 5 Requirements Gathering in Software Engineering: Process, Techniques, and Best Practices
- 6 Defining and Implementing a Requirements Baseline
- 7 Managing Project Scope — Why It Matters and Best Practices
- 8 How Long Do Requirements Take?
- 9 How to Reuse Requirements Across Multiple Products
- 4. Requirements Traceability
- Overview
- 1 What is Requirements Traceability? Importance Explained
- 2 Tracing Your Way to Success: The Crucial Role of Traceability in Modern Product and Systems Development
- 3 Bidirectional Traceability: What It Is and How to Implement It
- 4 What is Engineering Change Management (ECM)? A Complete Guide
- 5 Change Impact Analysis (CIA): A Short Guide for Effective Implementation
- 6 What is Meant by Version Control?
- 7 Key Traceability Challenges and Tips for Ensuring Accountability and Efficiency
- 8 The Role of a Data Thread in Product and Software Development
- 9 Unraveling the Digital Thread: Enhancing Connectivity and Efficiency
- 10 What is a Traceability Matrix? A Guide to Requirements Traceability
- 11 How to Create and Use a Requirements Traceability Matrix (RTM)
- 12 Traceability Matrix 101: Why It’s Not the Ultimate Solution for Managing Requirements
- 13 Live Traceability vs. After-the-Fact Traceability
- 14 Overcoming Barriers to Live Requirements Traceability™
- 15 Requirements Traceability, What Are You Missing?
- 16 Four Best Practices for Requirements Traceability
- 17 Requirements Traceability: Links in the Chain
- 18 What Are the Benefits of End-to-End Traceability During Product Development?
- 19 FAQs About Requirements Traceability
- 20 Product Traceability for Regulated Industries: A Complete Guide to Audit-Ready Compliance
- 5. Requirements Management Tools and Software
- Overview
- 1 Selecting the Right Requirements Management Tools and Software
- 2 Why Investing in Requirements Management Software Makes Business Sense During an Economic Downturn
- 3 Why Word and Excel Alone is Not Enough for Product, Software, and Systems Development
- 4 Can You Track Requirements in Excel?
- 5 What Is Application Lifecycle Management (ALM)?
- 6 Is There Life After DOORS®?
- 7 Can You Track Requirements in Jira?
- 8 Checklist: Selecting a Requirements Management Tool
- 6. Requirements Validation and Verification
- 7. Meeting Regulatory Compliance and Industry Standards
- Overview
- 1 Understanding ISO Standards
- 2 Understanding ISO/IEC 27001: A Guide to Information Security Management
- 3 What is DevSecOps? A Guide to Building Secure Software
- 4 Compliance Management
- 5 What Is Functional Safety (FuSa)? Standards, Lifecycle, and Where Programs Fail
- 6 What is FMEA? Failure Mode and Effects Analysis Guide
- 7 TÜV SÜD: Ensuring Safety, Quality, and Sustainability Worldwide
- 8 What is IEC 62443? A Guide to Industrial Cybersecurity
- 8. Systems Engineering
- Overview
- 1 What is Systems Engineering?
- 2 How Do Engineers Collaborate? A Guide to Streamlined Teamwork and Innovation
- 3 The Systems Engineering Body of Knowledge (SEBoK)
- 4 What Is MBSE? Model-Based Systems Engineering Explained
- 5 Digital Engineering Between Government and Contractors
- 6 Digital Engineering Tools: The Key to Driving Innovation and Efficiency in Complex Systems
- 9. Automotive Development
- Overview
- 1 Understanding IATF 16949: A Quick Guide to Automotive Quality Management
- 2 What Is ISO 21434? Automotive Cybersecurity Engineering Explained
- 3 What Is ISO 26262? A Guide to Functional Safety in Automotive
- 4 What Is ASIL? A Guide to Automotive Safety Integrity Levels in ISO 26262
- 5 What Is SOTIF? A Guide to ISO 21448 for ADAS Safety
- 10. Medical Device & Life Sciences Development
- Overview
- 1 The Importance of Benefit-Risk Analysis in Medical Device Development
- 2 Software as a Medical Device: Revolutionizing Healthcare
- 3 What’s a Design History File, and How Are DHFs Used by Product Teams?
- 4 Navigating the Risks of Software of Unknown Pedigree (SOUP) in the Medical Device & Life Sciences Industry
- 5 What Is ISO 13485? A Guide to Medical Device Quality Management Systems
- 6 What You Need to Know: ANSI/AAMI SW96:2023 — Medical Device Security
- 7 ISO 13485 vs ISO 9001: Understanding the Differences and Synergies
- 8 What Is IEC 62304? A Guide to Medical Device Software
- 9 What Is a Device Master Record (DMR)? Definition and FDA Requirements
- 10 Failure Modes, Effects, and Diagnostic Analysis (FMEDA) for Medical Devices: What You Need to Know
- 11 Embracing the Future of Healthcare: Exploring the Internet of Medical Things (IoMT)
- 12 What Is General Safety and Performance Requirements (GSPR)? What You Need To Know
- 13 What Is IEC 62366? A Guide to Medical Device Usability Engineering
- 11. Aerospace & Defense Development
- Overview
- 1 What Is ARP4754A? A Complete Guide to Civil Aircraft and Systems Development Assurance
- 2 Understanding ARP4761A: Guidelines for System Safety Assessment in Aerospace
- 3 What Is DO-254? A Complete Guide to Airborne Hardware Design Assurance
- 4 What Is DO-178C? A Complete Guide to Airborne Software Certification
- 12. Architecture, Engineering, and Construction (AEC industry) Development
- 13. Industrial Manufacturing & Machinery, Automation & Robotics, Consumer Electronics, and Energy
- 14. Semiconductor Development
- 15. AI in Product Development
- 16. Risk Management
- 17. Product Development Terms and Definitions
What Is DevSecOps? A Guide to Building Secure Software
Teams that treat security as part of daily engineering work, not a final gate, ship faster and spend less time on rework. That’s the core idea behind DevSecOps. For teams building complex, regulated products, DevSecOps produces audit-ready evidence as a natural byproduct of normal delivery. Getting there takes the right testing methods, pipeline design, and traceability practices.
This guide covers what DevSecOps is, how it differs from DevOps, the testing methods that support it, and best practices for implementation in regulated environments.
What Is DevSecOps?
DevSecOps, short for Development, Security, and Operations, is a software development methodology that treats security as a shared responsibility across engineering, security, and operations teams throughout the software development lifecycle (SDLC).
Instead of reviewing security at the end, teams codify security policies, automate security testing, and generate compliance evidence at every stage from first commit to production. Security configurations are version-controlled and peer-reviewed through the same workflows developers already use for application code.
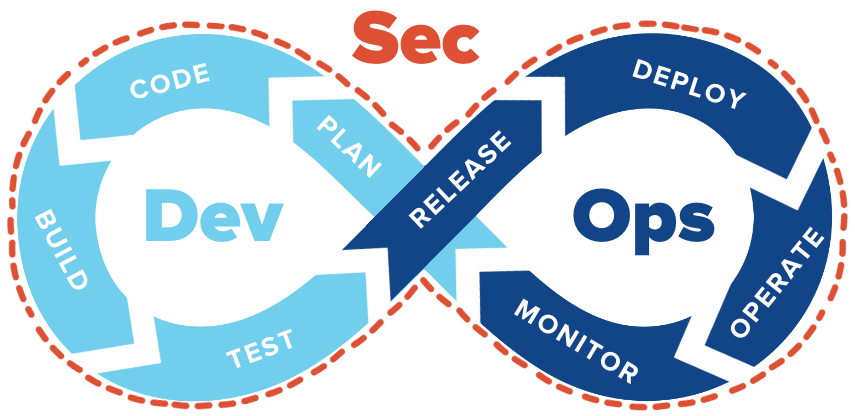
DevSecOps vs. DevOps
DevOps (Development and Operations) removes silos between development and operations to speed up delivery. DevSecOps extends that philosophy to security, moving it from a single checkpoint before release to automated scans at every pipeline stage. For teams building products under aviation standards like DO-178C or ISO 26262, deferring security to a final gate creates the same late-discovery problem their safety processes are designed to prevent.
Why Is DevSecOps Important?
DevSecOps builds security into the process from day one. Starting early reduces late-stage rework, keeps compliance evidence current, and catches vulnerabilities before they get expensive to fix.
Late-Stage Security Flaws Multiply Rework Costs
Software defects found in production cost far more to fix than the same flaws caught during development, and security vulnerabilities are no exception. Remediation costs spike after release because fixes trigger wider regression testing, field updates, and documentation updates.
A security flaw in an embedded medical device or avionics system doesn’t stay contained to the software team. It cascades through risk assessments, verification activities, design history files, and regulatory submissions.
AI-Generated Code Expands the Attack Surface
AI-assisted coding tools are accelerating delivery, but they’re also introducing new risks. Research shows that AI-generated code introduces security flaws in roughly half of cases. The bigger problem is speed: AI removes the bottlenecks (code review, debugging, team oversight) that used to catch vulnerabilities before production. Automated security scanning at every pipeline stage is one of the few ways to keep pace.
Disconnected Security Work Creates Traceability Gaps
Traceability is the ability to follow a requirement from its origin through design, implementation, and testing so you can prove each step was completed. In regulated programs, a security requirement that lives only in a compliance document creates a traceability gap. That gap works the same way as any other missing link in the V-model (the development lifecycle where requirements flow down through design and implementation, then back up through verification and validation).
When security controls can’t be traced to the requirements they satisfy, systems engineers end up rebuilding that evidence manually before audits.
Regulators Now Require Security-by-Design
Regulatory bodies increasingly mandate security-by-design. The FDA’s cybersecurity guidance for medical devices, issued June 2025, requires machine-readable Software Bills of Materials (SBOMs), secure update mechanisms, and traceability between cybersecurity controls and identified risks.
Aerospace programs under DO-178C, automotive teams under ISO 26262 and ISO/SAE 21434, and medical device teams under FDA guidance all face the same expectation. Compliance requires evidence of continuous security integration, not documentation assembled after the fact.
How Does DevSecOps Work?
DevSecOps typically combines shift-left and shift-right security practices, wired into CI/CD (continuous integration and continuous delivery) workflows so that findings turn into tracked engineering work.
Security Testing Runs at Both Ends of the Pipeline
Shift-left security moves testing to the earliest possible stage of development so teams catch defects while they’re still cheap to fix. Pre-commit hooks scan for exposed secrets, static analysis runs on every code commit, and dependency checks flag vulnerable libraries at build time.
Shift-right security extends monitoring into production through canary deployments (releasing changes to a small subset of users first), runtime vulnerability detection, and chaos engineering (deliberately injecting failures to test resilience). When production monitoring detects a new vulnerability pattern, that pattern feeds back into pre-deployment scans so future builds are automatically checked. This combination of shift-left and shift-right with continuous feedback is sometimes also referred to as “shift everywhere.”
Automation Keeps Pace With CI/CD Delivery
Manual security reviews can’t keep pace with CI/CD pipelines that build and deploy multiple times per day. Automated scans at each pipeline stage replace manual checkpoints, and policy gates can block a release when it violates organization-defined governance rules.
Policy-as-code frameworks like Open Policy Agent (OPA) codify those rules as version-controlled files that enforce standards automatically. The result is compliance automation built into the pipeline instead of a separate audit activity. AI-assisted security tools are adding another layer here, with machine learning models that prioritize scan findings by exploitability and suggest code fixes. When those findings connect back to requirements, teams can trace a vulnerability from detection through remediation and verification.
Findings Become Tracked Engineering Work
Security scan results only matter if they reach the right people and get resolved. The common approach is to route findings from scanning tools into existing issue trackers (Jira, Azure DevOps, GitLab Issues) so vulnerabilities are prioritized alongside other engineering work. A critical CVE in a production dependency might page the on-call engineer and block the next deploy, while a low-severity finding like a missing HTTP header enters the normal sprint backlog.
Testing Methods and Tools for DevSecOps
The scans referenced above fall into four categories of security testing, each designed to catch a different class of vulnerability. A mature DevSecOps pipeline runs all four, with one or more tools per category:
- Static Application Security Testing (SAST): Analyzes source code without executing the application to catch buffer overflows, SQL injection flaws, and insecure coding patterns. Common tools include SonarQube, Semgrep, and Checkmarx.
- Dynamic Application Security Testing (DAST): Tests running applications from an external perspective to surface runtime issues and deployment-specific vulnerabilities that SAST can’t detect. Tools like OWASP ZAP and Burp Suite Enterprise validate whether a flaw is actually exploitable.
- Software Composition Analysis (SCA): Checks third-party libraries and open-source dependencies against vulnerability databases like the National Vulnerability Database, and generates SBOMs for compliance. Common options are OWASP Dependency-Check, Snyk, and Trivy.
- Infrastructure as Code (IaC) scanning: Catches cloud and Kubernetes misconfigurations in Terraform, CloudFormation, and manifests by applying policy-as-code rules against frameworks like Center for Internet Security (CIS) Benchmarks. Checkov, Terrascan, and KICS are widely used for this.
Running all four requires coordination between security and engineering teams, which is where most organizations hit friction.
RELATED ARTICLE: A Practical Guide to Translating User Needs into Design Inputs
Ready to Find Out More?
Our team of experts is here to answer any questions and learn how we can help enable your continued success. Get started with a free 30-day trial, or book a demo!
Challenges of Implementing DevSecOps
The biggest DevSecOps adoption barriers are often cultural and organizational, though technical complexity plays a role too. Four problems come up repeatedly:
- Cultural resistance: Teams structured around handoffs between development, security, and operations create friction. If developers are measured on features shipped per sprint but not on scan pass rates or time-to-remediation, security remains someone else’s problem.
- Developer skill gaps: Many developers lack familiarity with common vulnerability classes and don’t see security as part of their role.
- Tool sprawl: Teams relying on too many disconnected tools lose findings between systems and spend more time on integration than on fixing actual vulnerabilities.
- Embedded systems complexity: Products with firmware, hardware-in-the-loop testing, and compliance scanning needs (MISRA C, CERT C) require specialized tools that don’t integrate well with DevSecOps toolchains built for cloud applications.
Addressing these barriers typically starts with culture and training before tooling, as the NIST SSDF framework in the best practices section below reinforces.
DevSecOps Best Practices
Any DevSecOps plan works when security requirements and compliance records get the same treatment as code: owned, versioned, reviewed, and traceable. Use these best practices as a checklist for getting there.
Build a Security-First Culture
NIST SP 800-218 (the Secure Software Development Framework, or SSDF) establishes that people and processes come before tools. The framework recommends assigning responsibility for secure development to specific roles, and role-based training must cover all personnel whose work affects security outcomes.
Security champions programs embed security expertise within development teams. A champion might review threat models during sprint planning, triage scan findings before they reach the central security team, or coach developers on fixing a recurring vulnerability class like insecure deserialization.
Use Threat Modeling to Define Security Requirements
Once teams have the culture and training in place, they need a structured way to figure out what to protect. Threat modeling is that process. Teams map out how an attacker could exploit the system, identify which components carry the most risk, and write security requirements based on those findings. This approach is also called “born left,” where security is designed into the system from the start instead of retrofitted later.
Without this step, the traceability chain starts from an incomplete set of requirements, and even perfect pipeline automation can’t fix that gap.
Integrate Security Into CI/CD Pipelines
Security tools belong at specific pipeline stages based on what they can detect and how expensive they are to run. Adding scans in a deliberate order instead of activating everything at once tends to produce better results:
- Pre-commit: Secrets detection and local IaC scanning keep credentials and obvious misconfigurations out of version control.
- Commit and build: SAST analyzes source code, SCA checks dependencies against vulnerability databases, and container images are scanned before registry push.
- Test and deploy: DAST validates running applications in staging, IaC scanning checks infrastructure changes, and policy gates block deployments that violate security policies.
- Production: Runtime monitoring, continuous vulnerability management, and certificate management keep the security posture current after release.
Pipeline hardening (securing the CI/CD infrastructure itself, independent of the code that flows through it) matters as much as scan coverage. Common steps include TLS-protected connections between source control and CI/CD, isolated builds on dedicated nodes, and manual approval before production deployment.
Establish Traceability From Requirements to Deployment
Requirements traceability works in both directions: forward traceability confirms that security requirements are implemented and tested, and backward traceability confirms that every implemented feature maps to an approved requirement. In regulated industries, this bidirectional chain is the foundation for proving DevSecOps compliance.
Jama Connect®, a requirements management platform for regulated product development, provides this through Live Traceability™. When a security requirement changes, every linked design element, test case, and implementation record is automatically flagged. Traceability Information Models (TIMs) define expected relationships between requirements, designs, and tests so that missing links surface before they become audit findings.
DevSecOps Builds Security Into the Development Process
Security gaps in regulated products form when security activities are disconnected from the workflows where engineering decisions happen. Skill gaps and cultural resistance compound the problem, but disconnection is what makes them expensive. DevSecOps closes that disconnect by making security a continuous, automated, and traceable part of every development phase.
For systems engineers, security requirements that trace through design, implementation, and verification produce the same documented proof that safety and compliance already demand. The practices described in this guide reduce review cycles, cut late-stage rework, and generate the documentation auditors expect. To see how Jama Connect fits your DevSecOps workflow, explore the platform.
Frequently Asked Questions About DevSecOps
What does DevSecOps stand for?
DevSecOps stands for Development, Security, and Operations. It extends the DevOps model by making security a shared responsibility across all three disciplines. In practice, teams write security requirements, automate security tests, and maintain security evidence alongside the rest of the delivery workflow.
What is the difference between DevSecOps and DevOps?
DevOps removes silos between development and operations to speed delivery. DevSecOps adds security as a continuous activity at every pipeline stage. In a DevOps pipeline, security testing often happens once before deployment, while DevSecOps runs scans at commit, build, test, deploy, and production stages.
What tools are used in DevSecOps?
DevSecOps toolchains typically include SAST tools (SonarQube, Checkmarx, Semgrep) for static code analysis, DAST tools (OWASP ZAP, Burp Suite Enterprise) for runtime testing, SCA tools (Snyk, OWASP Dependency-Check, Trivy) for dependency vulnerability scanning, and IaC scanners (Checkov, Terrascan, KICS) for infrastructure misconfiguration checks. For regulated teams, scan findings also feed into requirements management platforms like Jama Connect to maintain traceability.
Is DevSecOps required for regulatory compliance?
Regulatory bodies increasingly mandate the practices behind DevSecOps without always using the term. The FDA now requires traceable cybersecurity controls and SBOMs for medical devices, DO-178C requires traceability at higher assurance levels, and ISO 26262 paired with ISO/SAE 21434 requires coordinated safety and cybersecurity workflows in automotive. Even where DevSecOps isn’t named explicitly, the underlying expectations (traceability, automation, continuous evidence) are becoming standard.
How is AI used in DevSecOps?
AI is increasingly used to triage security findings, flag the most exploitable vulnerabilities first, and recommend fixes directly in developer workflows. Some CI/CD platforms now offer AI-powered analysis that reduces false positives and speeds up remediation. These capabilities are evolving quickly but currently work best alongside traditional scanning tools like SAST, DAST, and SCA. Regardless of how a vulnerability is found, it still needs to trace back to a requirement through a platform like Jama Connect so teams can verify the fix.
Learn Best Practices for Live Traceability™ In This Webinar
DevSecOps seeks to establish a security culture that guarantees the software is secure and complies with compliance standards by integrating security into every phase of the software development lifecycle, from planning through deployment.
Book a Demo
See Jama Connect in Action!
Our Jama Connect experts are ready to guide you through a personalized demo, answer your questions, and show you how Jama Connect can help you identify risks, improve cross-team collaboration, and drive faster time to market.