This blog previews our recent webinar. To watch the entire presentation, visit: “Systems Engineering 101: Building a Strong Foundation for Your Career.”
New to Systems Engineering in Medical Device & Life Sciences? Here’s What You Need to Know.
Stepping into systems engineering for the first time, transitioning into a new role, or looking to strengthen your foundation and grow with confidence? This webinar will help you build a clear understanding of what systems engineering is, what the day-to-day work looks like, and what it takes to succeed.
In this webinar, Chris Unger, INCOSE Healthcare Working Group Lead, and Vincent Balgos, Sr. Director of Solutions & Consulting at Jama Software, share practical guidance for getting started and building a strong foundation for long-term career growth in the medical device & life sciences industry. From core responsibilities and daily work to the hard and soft skills that matter most, this session will help you better understand the role and how to grow in it.
What You’ll Learn:
- What systems engineers do day to day, and the core responsibilities of the role
- The essential hard and soft skills that help systems engineers succeed
- Practical guidance for navigating a new or evolving systems engineering role
- Strategies to keep learning, growing, and building confidence in your career
- Real-world insights from experienced systems engineers you can apply right away
- Take the first step in your systems engineering journey and register today.
WEBINAR PREVIEW – WATCH ENTIRE PRESENTATION HERE
TRANSCRIPT BELOW
Vincent Balgos: Thank you for attending. My name is Vincent Balgos. I’m the Senior Director of Medical Device Solutions here at Jama Software. And today I’m happy to have a conversation with Chris Unger. Chris, would you like to introduce yourself?
Chris Unger: Yeah. Hi, I’m Chris Unger, the retired Chief Systems Engineer for GEA Healthcare. I spent five years in defense and then 40 years in medical device, and I’m the head of the INCOSE Healthcare Working Group.
Balgos: Great. And Chris, we just finished up with the 11th annual systems engineer, sorry, INCOSE Systems Engineering Conference. I’m curious, could you share with our audience a little bit about the history, but also what exciting events and key takeaways that you had from this year’s event?
Unger: Sure, absolutely. Thank you, Vincent. Yeah, we started 11 years ago in Chicago when AAMI created the TIR45, on how to be agile in healthcare while working with the FDA. And we had a concern that would be considered software only. We wanted to have more iterative spiral development. And it was 15 people just by invitation only, and it has grown now to the last two years of over 200 people and many, many tracks. And particularly exciting to see the evolution in topics. For example, compliance was one of our early topics, and now it’s not there. We don’t worry about compliance. What we’re interested about is customer focus, and the AI track has grown from 10 people to 50 people in the room. So very exciting evolution of topics.
RELATED: Jama Connect® for Medical Device Development
Balgos: Yeah. Where do you see systems engineering growing within the MedTech area?
Unger: Yeah. Compared to 40 years ago, devices were fairly complex. CT had hardware and software, hardware chemistry and mechanics, and electronics, and some software to now, with the growth of software, it is incredibly complex. Layers, you’ve got algorithms, four levels of control theory, and so many overconstraints. So that’s where to take, for example, a thermal problem. Is that a dissipation problem in electronics? Is it a thermal cooling problem? Is it a duty cycle problem of like, “I’m spending too much time in high performance, and I should coach the customer in only using the high dissipation modes.” So those kinds of system trade-offs are becoming much more important, but that’s the baseline of the last five years. Going forward with AI, the implementation speed’s going to go way, way higher. I even saw that 10 years ago, when we had more of the beginning of the digital twin.
In the past, mechanical engineers had time to do a design, ship it out, and get it back. Now it’s like with digital twin, they do it at a design, and they get the answer back the next day. So you really did need to make sure that you understood the incremental approach to avoid rework. AI is going to take that to the next level. The ability to have AI do your circuit science for you, do your software design, the speed’s going to go up like 10X, and systems engineering has to go off and be the orchestrator, the conductor of the orchestra, make sure when everybody’s going so fast, we still stay aligned and focused on the customer.
So in those cases, being able to work with marketing, trust marketing, but also know the customer’s needs and be able to take the value to the customer, divided by being pseudo-analytical, divided by the cost to implement times the risk. Something might take a certain amount of effort and have a 10% chance of succeeding. So the effective cost of the company is 10X bigger. Being able to tie that all together and make sure everybody is focused on the most valuable work for the next week, not the next six months. The speed of those decisions is going to be huge going forward.
RELATED: LEX Diagnostics Boosts Efficiency by Modernizing its Requirements Tool with Jama Connect
Balgos: Yeah. And that system thinking approach is what really brings system engineers here to help-
Unger: Sorry to interrupt. But systems thinking plus the ability to communicate it in words, taking the customer’s needs and translating that down into words that an electrical software engineer can understand. That translation, speaking both worlds together, is critical.
Balgos: So yeah, not just thinking, but then translating and helping drive these more AI-enabled teams to make quicker decisions and safer and more effective healthcare products. Great. Anything else on the AI front that excites you with MedTech coming up?
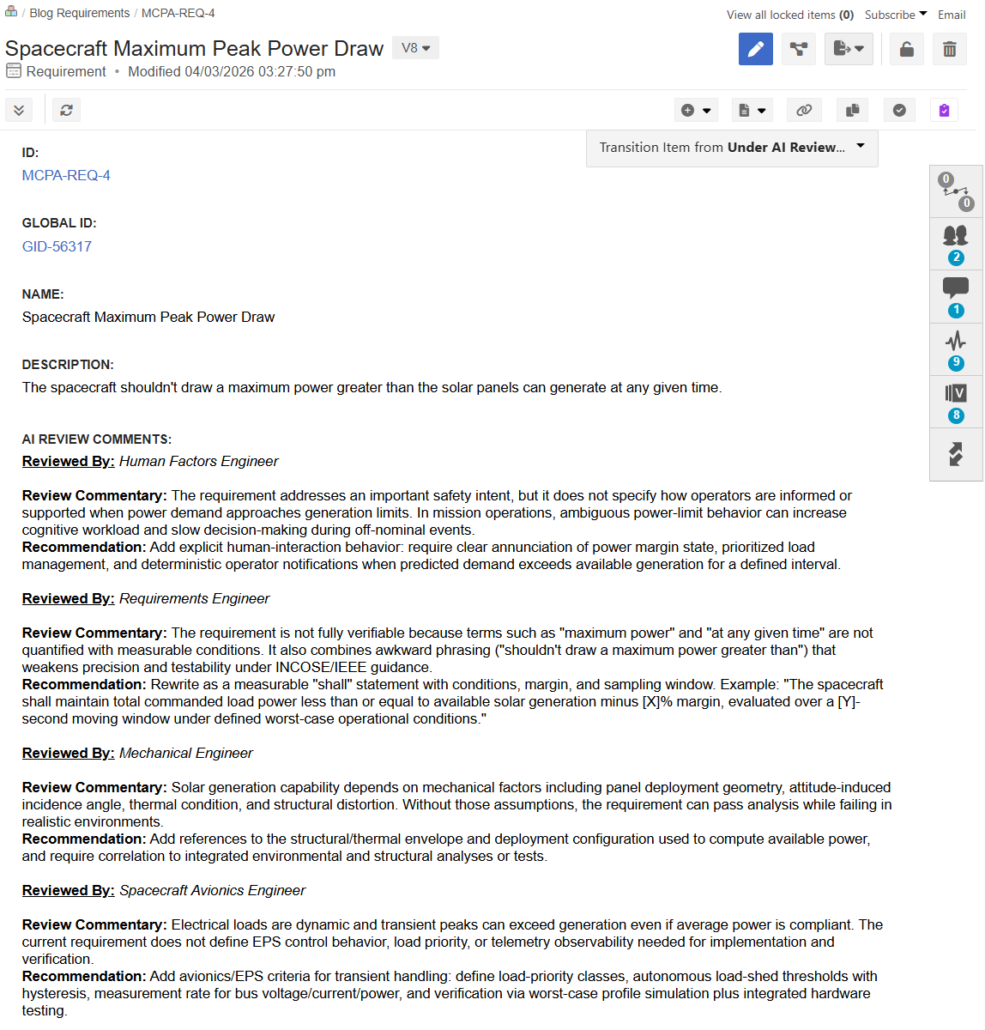
Unger: Yeah. The ability to have AI take some of the tedious work out, how to write a good requirement, A, can do that really well. It’s also really easy to learn new techniques. I was talking to the CEO of a startup about a use case, and that’s something that software people use for a while, systems people didn’t, and she didn’t understand what it was. So she was trying to get an example for a company, and she gave AI, “Give me a use case for an infusion pump in this problem.” And it gave her a 10-page report, really good quality, not AI, which doesn’t know what infusion up is. So the ability to say, “Oh, I’d like to learn this technique. Can you do this for me?” Your speed of learning will be really fast. The problem then is you’ve got to make sure that you know how to review those things.
So again, the ability to do good reviews and have good conversations with people is the skill you need now. I was talking about with a engineer, that example of the board where we didn’t use four boards to one, what’s the effect on thermal flow? What’s the effect on EMI/MC? Did you take a lot of EMC and suddenly put it into one area, so the EMC issue is bigger? That kind of skill that you should be using to converse with engineers who are brilliant in their area, but don’t understand other areas, will be much more important even when talking to the AI agents.