What is the Department of Energy National Cyber-Informed Engineering Strategy (CIE) Framework?
Cybersecurity incidents have become significant in recent years, causing ripple effects across countries and communities. Regulating cybersecurity has often fallen to private entities. However, with recent cyberattacks causing large-scale impacts, government agencies are now setting forth new actions and regulations.
The US Department of Energy recently released the National Cyber-Informed Engineering Strategy (CIE) Framework to address mounting cybersecurity concerns. In this blog, we will overview this newly released framework and briefly discuss how risk management can help energy companies by making them better positioned to manufacture and maintain the tools that help prevent and quickly recover from cyberattacks.
RELATED: 5 FBI Recommendations for Medical Device Cybersecurity
Department of Energy National Cyber-Informed Engineering Strategy (CIE) Framework
The U.S. energy sector faces continuous and ever-evolving cybersecurity threats, among various other industries. According to the 2022 Office of the Director of National Intelligence (DNI) Annual Threat Assessment, “our adversaries maintain capabilities to launch cyberattacks that could disrupt critical infrastructure, including industrial control systems in the U.S. energy sector. Cybersecurity attacks on critical infrastructure are particularly consequential and ensuring the security, reliability, and resilience of these systems is a top priority for the U.S. Department of Energy’s (DOE) Office of Cybersecurity, Energy Security, and Emergency Response (CESER) and its partners in government and the private sector”
The CIE framework, grown from earlier Congressional direction regarding threats to the nation’s energy sector, advocates for an evolutionary shift across the energy industry and related institutions, including researchers, standards bodies, Federal partners, and others. Its recommendations reflect expertise and insight from energy companies, energy systems and cybersecurity manufacturers, standards bodies, researchers, DOE National Laboratories, and Federal partners in the cybersecurity and engineering mission space.
It encourages the adoption of a “security-by-design” mindset within the Energy Sector Industrial Base, which refers to building cybersecurity into our energy systems at the earliest possible stages rather than trying to secure these critical systems after deployment.
Principles of Cyber-Informed Engineering (CIE): A Five-Pillar Approach
The CIE Strategy is built upon five pillars. When united, CIE’s pillars create an overall approach that enables “a body of knowledge, a diverse and expanded workforce, and the engineering and manufacturing capacity to apply CIE to today’s energy infrastructure and to engineer future energy systems to eliminate or reduce the ability of a cyber-enabled attack to generate significant impact.”
These five pillars are:
- Awareness
- Education
- Development
- Current infrastructure
- Future Infrastructure
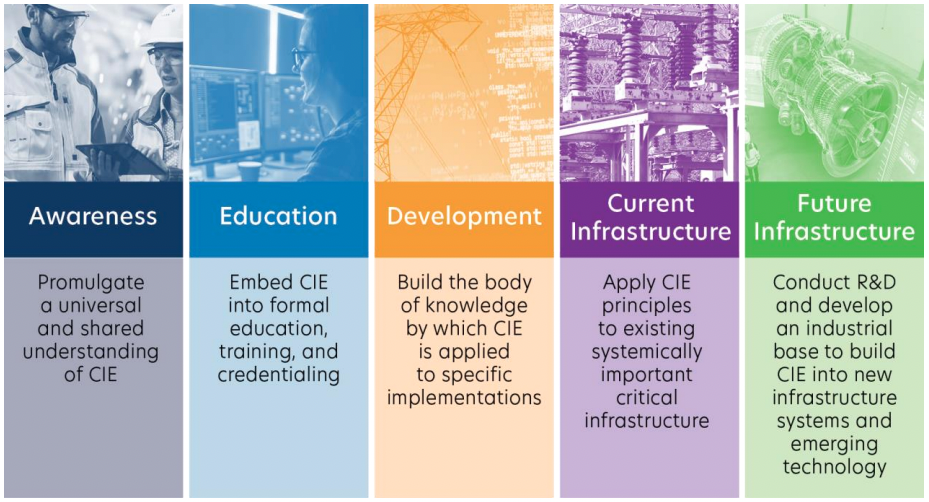
Image from CIE Strategy
RELATED: What is the Urgency Behind Automotive Cybersecurity?
Using CIE As a Model for Other Critical Infrastructure Sectors
While this National Cyber-Informed Engineering Strategy has been developed for energy sector systems, the strategy can serve as a guide for other critical infrastructure sectors to adopt.
CIE concepts and strategies to apply various types of engineering. It represents foundational engineering principles that apply similarly to all other critical sectors—such as water, transportation, telecommunications, manufacturing, and more.
Risk Management Agencies, other federal agencies, and critical infrastructure partners and stakeholders “can leverage the National CIE Strategy as a model to implement CIE principles broadly to all U.S. infrastructure systems that operate critical functions for the nation,” U.S. Department of Energy.
How Jama Connect Can Enable Cybersecurity with Our Risk Module Framework
Jama Connect enables organizations to identify and manage cyber-related risks with cybersecurity requirement management, test case and test execution management, work product verification management, software tool qualification support, configuration management, change control, and tool ecosystem integration.
To learn more, download our Jama Connect Datasheet.
- Euro Roundup: MDCG Publishes Guidance on MDR, IVDR Authorized Representative Requirements - December 12, 2022
- 2023 Predictions for Aerospace & Defense Product Development - December 8, 2022
- 2023 Predictions for Product & Systems Development Teams - December 1, 2022