What Is the Systems Engineering Process? A Guide for Complex Programs
The best-run complex programs share a common trait. They use a structured systems engineering process to keep hardware, software, and human factors teams aligned from concept through retirement. That alignment comes from having clear interfaces between disciplines and verification evidence that stays connected at every level.
We’ve seen this across aerospace, defense, automotive, and medical device programs. Teams that invest early in structured requirements and traceability catch conflicts before integration and keep compliance evidence audit-ready. Without that investment, gaps tend to surface at the worst possible time.
This guide covers what the systems engineering process is, the key phases and lifecycle frameworks, how requirements management and the V-Model support it, and where teams most commonly run into trouble.
What Is the Systems Engineering Process?
A systems engineering process is a cross-discipline approach to making sure hardware, software, personnel, and procedures all work together across the full lifecycle of a complex product or system. Most engineering disciplines go deep in one domain. Systems engineering works across all of them, managing the tradeoffs between disciplines and defining the interfaces that connect them. When a satellite program has 15 subsystem teams in parallel, someone needs to make sure the thermal engineer’s constraints don’t conflict with the power engineer’s allocation.
Most failures in complex programs trace back to broken relationships between requirements, interfaces, and verification activities. That’s what the process is for. It keeps those connections intact so problems don’t show up for the first time during testing or an audit.
Why a Systems Engineering Process Is Important
Programs that spent under 5% of total cost on requirements engineering experienced 80% to 200% cost overruns, while those investing 8% to 14% met their budgets. Incomplete requirements are one of the most common reasons projects fail or stall. The specifics look different across industries, but it always comes back to the same thing. If teams don’t get requirements right early, they pay for it later.
For teams building regulated products, the consequences go beyond budget. Defense program audits have found cases where programs couldn’t show a clear link between their requirements and the work they actually delivered. When requirement baselines drift and interfaces get defined in different places, traceability gaps turn into compliance problems that take months to close.
Key Frameworks and Standards
If you’re working in defense, automotive, or medical devices, you’ll run into these frameworks repeatedly:
- ISO/IEC/IEEE 15288:2023: Establishes a common framework for describing the lifecycle of engineered systems from conception through disposal, without prescribing a specific methodology.
- International Council on Systems Engineering (INCOSE) SE Handbook v5.0: Provides practical application guidance for 15288’s processes across automotive, defense, healthcare, and other domains.
- IEEE 15288.1: Establishes systems engineering requirements intended to form the basis of acquirer-supplier agreements for Department of Defense (DoD) programs.
- NASA Systems Engineering Handbook: Provides implementation guidance for NASA programs and is one of the most widely referenced SE handbooks in practice.
These standards give teams shared definitions for the practices that break down first under pressure, including requirement baselines, interface control, verification planning, and traceability.
Key Phases of the Systems Engineering Process
ISO/IEC/IEEE 15288 defines 14 technical processes, not rigid sequential phases. The phases below line up with those processes, and systems engineering teams repeat them at every level of the system hierarchy. That’s why requirement and traceability failures are rarely isolated to one milestone.
Concept Exploration and Requirements Definition
Teams define the system’s purpose by identifying who will use, operate, regulate, and maintain it, then developing the Concept of Operations (ConOps) and establishing requirements baselines. Stakeholder identification goes well beyond end users to include program managers, regulators, and anyone with approval authority. If a stakeholder class gets missed here, it tends to surface later as a change request or a verification gap.
Functional Analysis and Allocation
With the purpose defined, teams break system functions into sub-functions, allocate requirements to functional elements, and define the interfaces between them. Trade studies evaluate allocation alternatives. Hidden conflicts start at this stage if allocation decisions are made without clear ownership and interface control, because teams can move fast in parallel and still drift apart if those allocations aren’t visible across the system.
Design Synthesis
Preliminary Design Review (PDR) and Critical Design Review (CDR) are the key decision gates. Teams turn the functional and logical design into a physical architecture and produce the detailed design specs and interface control documents that will guide the build. Weak upstream definition starts getting expensive at this point, because a vague requirement from concept exploration now affects architecture, interfaces, and review readiness.
Implementation and Integration
Configuration and interface control become critical as teams build, code, or procure system elements and start putting them together. Many teams first feel the cost of earlier process gaps here. The integration issue looks immediate, but the cause is often an outdated baseline or an unreviewed change from earlier in the lifecycle.
Verification and Validation
These are separate processes with different objectives. Verification confirms that system elements meet specified requirements (“built right”), while validation confirms the full system actually works the way users and operators need it to (“built the right thing”). Teams struggle here when they try to reconstruct verification evidence after the fact, because weak requirement relationships upstream turn the problem from testing into an evidence gap.
Operations, Maintenance, and Retirement
Systems engineering doesn’t end at release, and neither do traceability obligations. When a mid-life upgrade is planned, engineering activities revisit earlier lifecycle stages depending on the scope. Mature programs still manage changed requirements, updated verification evidence, and new baselines long after initial deployment.
The Role of Requirements Management in Systems Engineering
Requirements management runs through every phase of the systems engineering process and is how teams keep the system definition current while multiple disciplines work at once. This means tracking every requirement from origin through design, implementation, and verification. When a requirement changes, every linked test case, design element, and risk assessment needs updating. Bidirectional traceability is what makes that tracking reliable at scale.
Complex systems can have thousands of requirements across multiple levels for dozens of products. At a small scale, manual traceability feels survivable. At program scale, it becomes a recurring tax on systems engineering, quality, and verification teams, and it still leaves gaps.
The V-Model in Systems Engineering
The V-Model covers the development stage specifically. The left side represents top-down decomposition, where stakeholder needs flow down through system requirements, subsystem specifications, and build-to documentation. The right side represents bottom-up integration and verification, from unit testing up through system-level validation. Teams create verification plans on the left side at the same time as requirements. If verification planning is deferred, teams create the late-stage surprises they end up blaming on integration.
Traceability Across the V
Each left-side definition level maps horizontally to a right-side verification level. Stakeholder needs map to acceptance validation, system requirements to system verification, and so on down to unit level. This correspondence is what distinguishes teams that catch integration problems early from those that don’t. Teams need those connections maintained continuously, not reconciled manually near a milestone.
Other Lifecycle Models
Incremental approaches deliver partial capability earlier, while agile methods like the Scaled Agile Framework (SAFe) manage the tension through Solution Intent, where system requirements evolve alongside the system. The specific lifecycle model a team chooses isn’t what determines success. Every model still has to answer the same questions about baseline control, decomposition, traceability, and verification.
Model-Based Systems Engineering (MBSE)
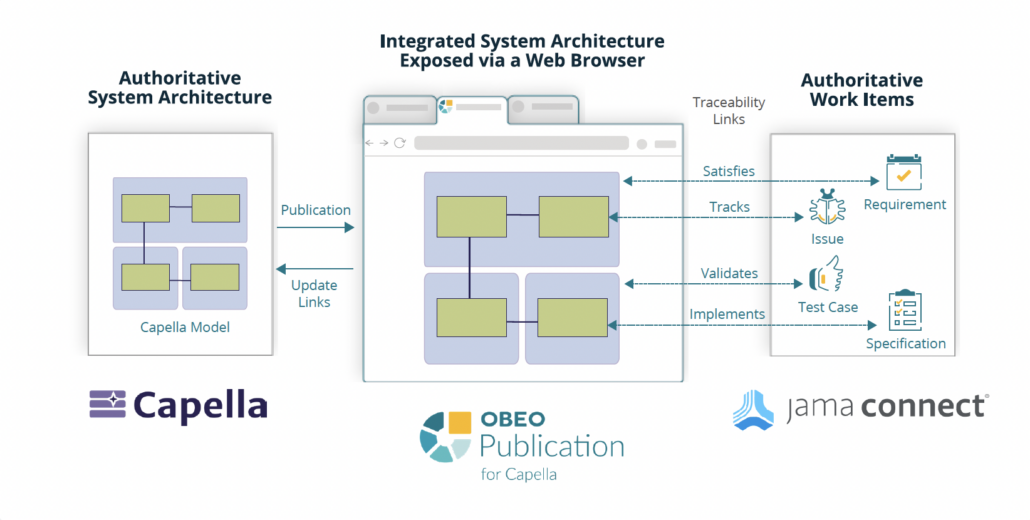
Traditional systems engineering relies on disconnected documents where requirements live in one tool and design models live in another. Model-Based Systems Engineering (MBSE) replaces that fragmented approach with a unified model that supports requirements, design, analysis, and verification activities across the lifecycle. The primary modeling language, Systems Modeling Language (SysML), reached v2.0 with formal Object Management Group (OMG) adoption in July 2025.
MBSE is gaining real traction across the industry, though published studies still have limited data on how much it saves at the program level. What matters in practice is whether the approach, documents or models, actually helps teams catch inconsistencies earlier and keep their requirements under control.
Common Challenges in the Systems Engineering Process
Three recurring failure patterns show up when teams underinvest in these processes:
- Requirements drift and traceability gaps: When requirements change but downstream artifacts don’t get updated, gaps accumulate silently. GAO audits have repeatedly found traceability issues with defense program baselines, with corrective actions sometimes taking over a year to complete.
- Siloed teams and tool fragmentation: When requirements live in disconnected systems, bidirectional traceability becomes manually intensive and error-prone. The relationships between artifacts become harder to trust as those tools multiply.
- Scaling across multi-discipline programs: The number of handoffs between requirements owners, subsystem teams, system architects, and verification engineers grows fast with program size. What worked with one team starts to break when the coordination surface expands faster than the process does.
All three point to the same underlying problem. The connections between requirements, design artifacts, and verification evidence are either missing or too expensive to maintain manually.
How Jama Connect Supports the Systems Engineering Process
Across every phase of the systems engineering process, the need is the same. Teams have to keep their requirements, design decisions, and verification evidence connected and up to date. When those connections break or go stale, the cost shows up at integration, audit, or both.
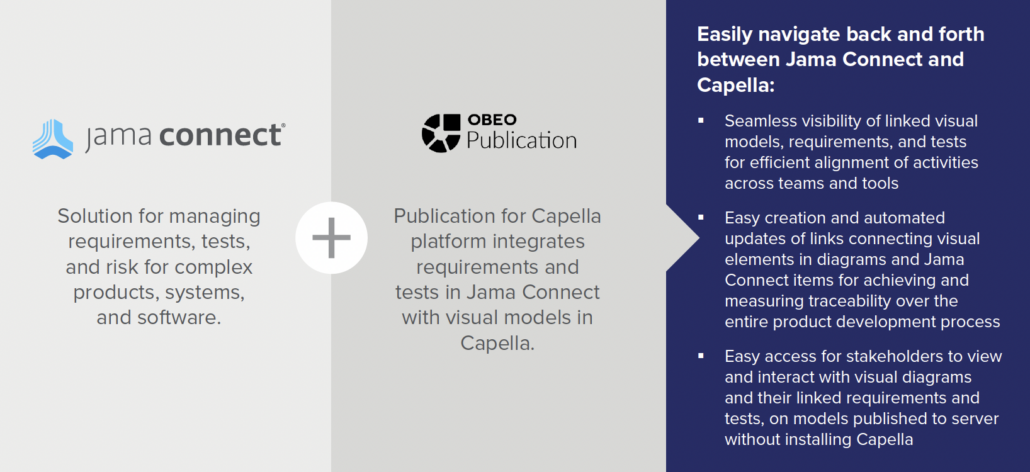
Jama Connect® is a requirements management and traceability platform that supports this workflow through Live Traceability™, which flags affected downstream items when requirements change so teams can assess impact and preserve the decision trail for audits. Traceability Information Models give teams pre-built frameworks for standards like ISO 13485, DO-178C, and ISO 26262, so missing downstream artifacts get flagged automatically. Start a free 30-day trial to see how it fits your workflow.
Frequently Asked Questions About the Systems Engineering Process
What is the difference between systems engineering and software engineering?
Software engineering goes deep within one domain. Systems engineering works horizontally across hardware, software, and human factors. A systems engineer manages the interfaces and tradeoffs between those disciplines to make sure a local improvement doesn’t create a problem elsewhere in the system.
What does a systems engineer do?
A systems engineer leads the concept of operations, defines and allocates requirements, evaluates tradeoffs, manages interfaces, and oversees verification and validation. They work across the full lifecycle from concept through retirement and make sure no team improves their piece at the expense of the whole.
What industries use the systems engineering process?
Aerospace and defense, automotive, medical devices, semiconductor, and energy are the most common verticals. Any industry building complex, multi-discipline products with regulatory or safety requirements tends to rely on a structured systems engineering process.
How does systems engineering relate to project management?
Project management handles schedule, cost, and resources. Systems engineering handles the technical content, including requirements, architecture, interfaces, and verification. They’re complementary disciplines that coordinate closely on complex programs.

 What Is the Cost of Poor Quality (COPQ)? How to Calculate and Reduce COPQ
What Is the Cost of Poor Quality (COPQ)? How to Calculate and Reduce COPQ