Editors Note: This post on safety and security in in automotive development is a guest post by from our partner Ansys. To learn more about Ansys, visit their website.
Safety and security have always represented a driving force in automotive engineering. Today, these performance criteria are more important than ever, as vehicles continue to grow exponentially in technological complexity. Advanced technologies deliver benefits, but also create new risks and potential failure modes.
With sales of electric vehicles projected to reach $567 billion by 20251, the design of powertrains and battery management systems has been brought to the forefront. Automakers also hope to capture a share of the global autonomous vehicle market, which will account for $556.67 billion by 20262, placing more focus on embedded control software, perception systems and sensors.
Before these diverse innovations can be commercialized, they must be analyzed and verified for reliable performance under every operating condition. Equally important, all electronics must be proven to work together at the system level, which means developing a robust system-level architecture, testing every integration point, and identifying and addressing weaknesses.
The Industry’s Leading Software for Automotive Modeling, Analysis and Simulation
Mastering these diverse, complex automotive engineering tasks may seem overwhelming ― or even impossible ― but there is good news. An established leader in engineering simulation for over 50 years, Ansys enables automakers to navigate the complex design and verification challenges associated with electrification, ADAS and other technology advancements.
The depth and breadth of the Ansys portfolio mirrors the complexity of today’s vehicle designs ― bringing modeling, analysis and simulation together in a robust, connected platform. From physics-based simulations that focus on crash-worthiness to the verification of embedded software, sensors, cameras and radars, Ansys solutions help automakers analyze every component in today’s cars.
RELATED: Watch a demonstration of the Jama Connect for Automotive Solution
Navigating the Unique Challenges of Safety and Security
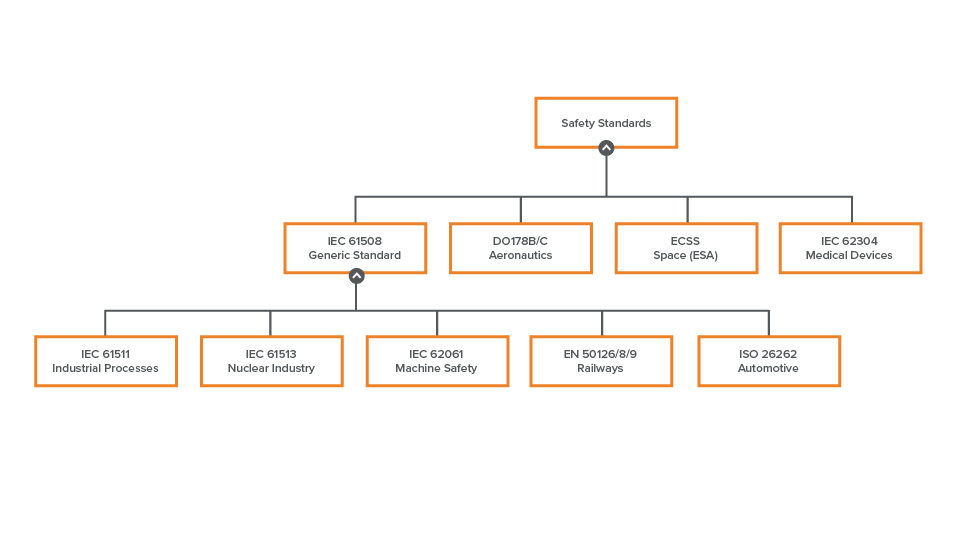
Regarding electronics safety and security, software from Ansys helps automotive engineers by supporting safe software development, functional safety analysis and cybersecurity analysis.
Safer Embedded Software Development
Underlying the advanced electronic systems found in modern cars are millions of lines of embedded software code that ensure their flawless operation under every driving scenario. Ensuring that the overall software model, and every line of code, deliver the desired functionality is critical to protecting the safety of human passengers. To meet the highest safety standards and comply with regulatory guidelines, software engineers must subject this code to rigorous testing.
With Ansys SCADE, engineers can streamline design and verification processes via automatic code generation of ISO 26262 critical software up to ASIL D. SCADE can be easily integrated into existing AUTOSAR development flows for software components, eliminating time-consuming manual reviews.
For example, as Subaru created control software code for its first hybrid vehicle, it automated 95% of the development process by relying on Ansys SCADE to generate code for the car’s innovative engine, called the e-BOXER. Today, it only takes Subaru engineers half a day to implement a model for the e-BOXER’s electronic control unit (ECU) once the control logic has been defined. This enables Subaru’s developers to modify the ECU’s logic and architecture much more frequently and easily as they explore continuing design innovations.
Explore how automakers are improving the accuracy and speed of embedded software development by 50%.
Robust, Automated Safety Analysis
Functional safety analysis ensures that automotive electronics deliver reliable performance over time, without system failures leading to unreasonable risk. This analysis must encompass the entire electronics architecture, including down to the chip level.
Ansys medini analyze streamlines and automates functional safety analysis via a model-based environment that supports executing the safety-related activities required by applicable standards like ISO 26262. It has helped many customers reduce time and costs, without sacrificing analytic rigor.
For example, LiTHIUM BALANCE develops battery management system (BMS) solutions for electric vehicles in keeping with the most stringent safety, performance and reliability standards. By leveraging medini analyze, engineers at LiTHIUM BALANCE quickly and affordably manage the functional safety verification of their BMS designs.
By providing an easy-to-understand, visual representation of complex electronics and their integration points, Ansys has benefited ZF Friedrichshafen AG, a global technology company that supplies systems to automakers. Ansys medini analyze has streamlined and accelerated functional safety analysis for hardware, software and systems ― delivering possible efficiencies including an up to 50% reduction in the time devoted to these tasks.
The emergence of automated driving has brought an even greater challenge: What if components such as sensors are working as designed, but their capabilities fall short under real-world conditions? A new standard, ISO 21448, focuses on safety of the intended functionality (SOTIF). Ansys medini analyze helps engineers not only identify weaknesses, triggering conditions and causal effects, but also interfaces with simulation and testing tools to validate perception software and other ADAS components.
Ready to take your safety case to the next level? Request an Ansys medini trial.
Rigorous Cybersecurity Analysis
The increased amount of software and connectivity in cars has made them vulnerable to cyberattacks. Recent headlines, as well as the ISO 21434 cybersecurity standard, have made cybersecurity analysis an essential part of the automotive development process.
Ansys medini analyze for Cybersecurity addresses system-level security via an easy-to-use modeling and analysis environment, ensuring that the complex electronics architecture is impervious to attacks. By quickly identifying and addressing potential threats and vulnerabilities, engineers can deliver secure products, reduce time to market, maximize profits and comply with upcoming cybersecurity regulations.
A Partnership That Delivers Added Value
Today many automotive leaders are applying Ansys solutions, while also leveraging Jama Connect for product development. A value-added partnership between these companies means that Jama customers can seamlessly and directly integrate Ansys SCADE and Ansys medini analyze. For the first time, the automotive electronics development and testing process is supported by a linked set of industry-leading software tools.
To learn more about the benefits of this partnership, watch our recent webinar or review our white paper.